Google Workspace
You can integrate a Google Workspace (formerly Google Suite) account with Cloudflare Access. Unlike the instructions for generic Google authentication , the steps below will allow you to pull group membership information from your Google Workspace account.
Once integrated, users will login with their Google Workspace credentials to reach resources protected by Cloudflare Access or to enroll their device into Cloudflare Gateway.
Please note that you don’t need to be a Google Cloud Platform user to integrate Google Workspace as an identity provider with Cloudflare Zero Trust. You will only need to open the Google Cloud Platform to access settings for your OIDC identity provider.
-
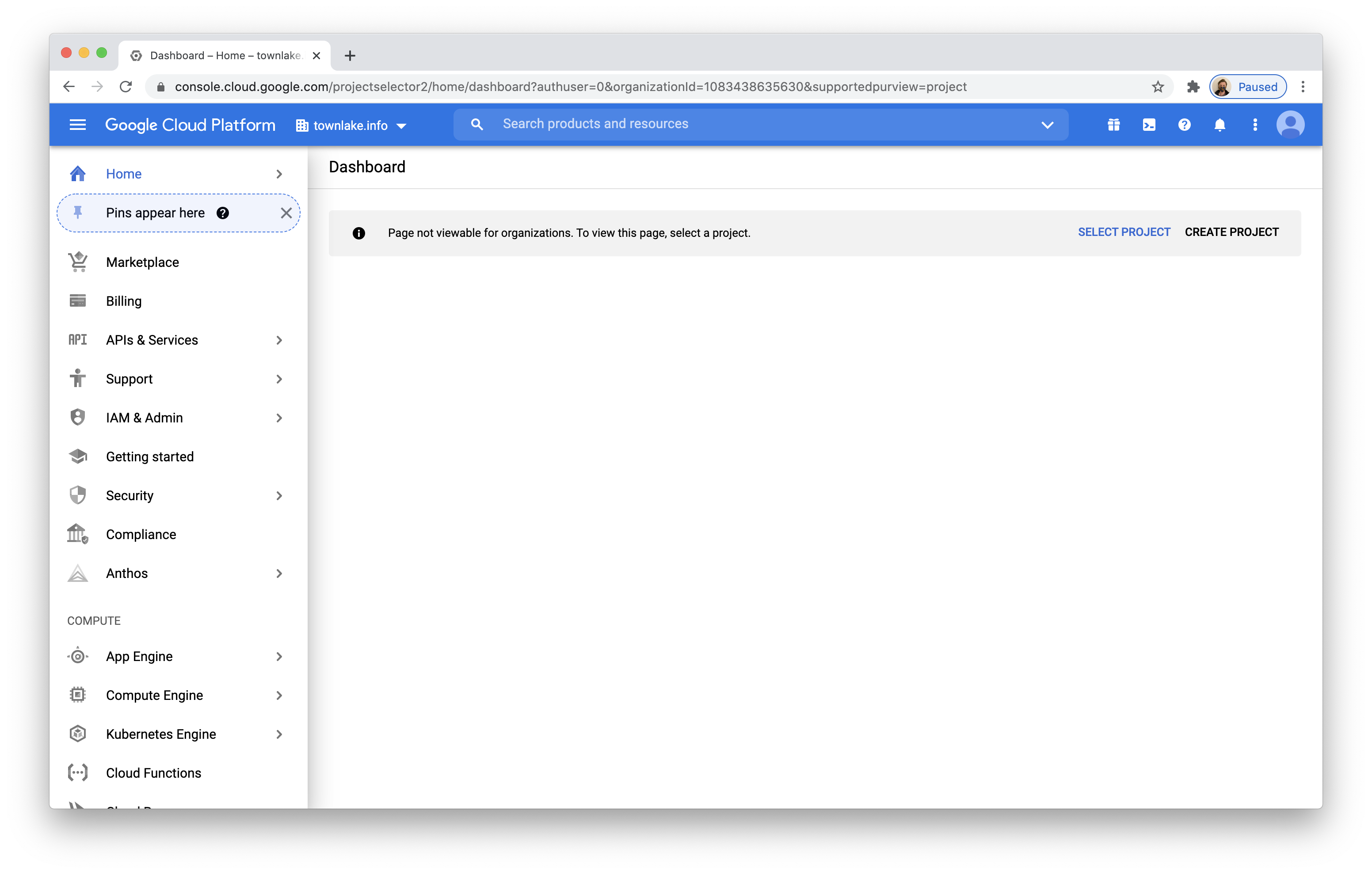
Log into the Google Cloud Platform console. This is separate from your Google Workspace console.
-
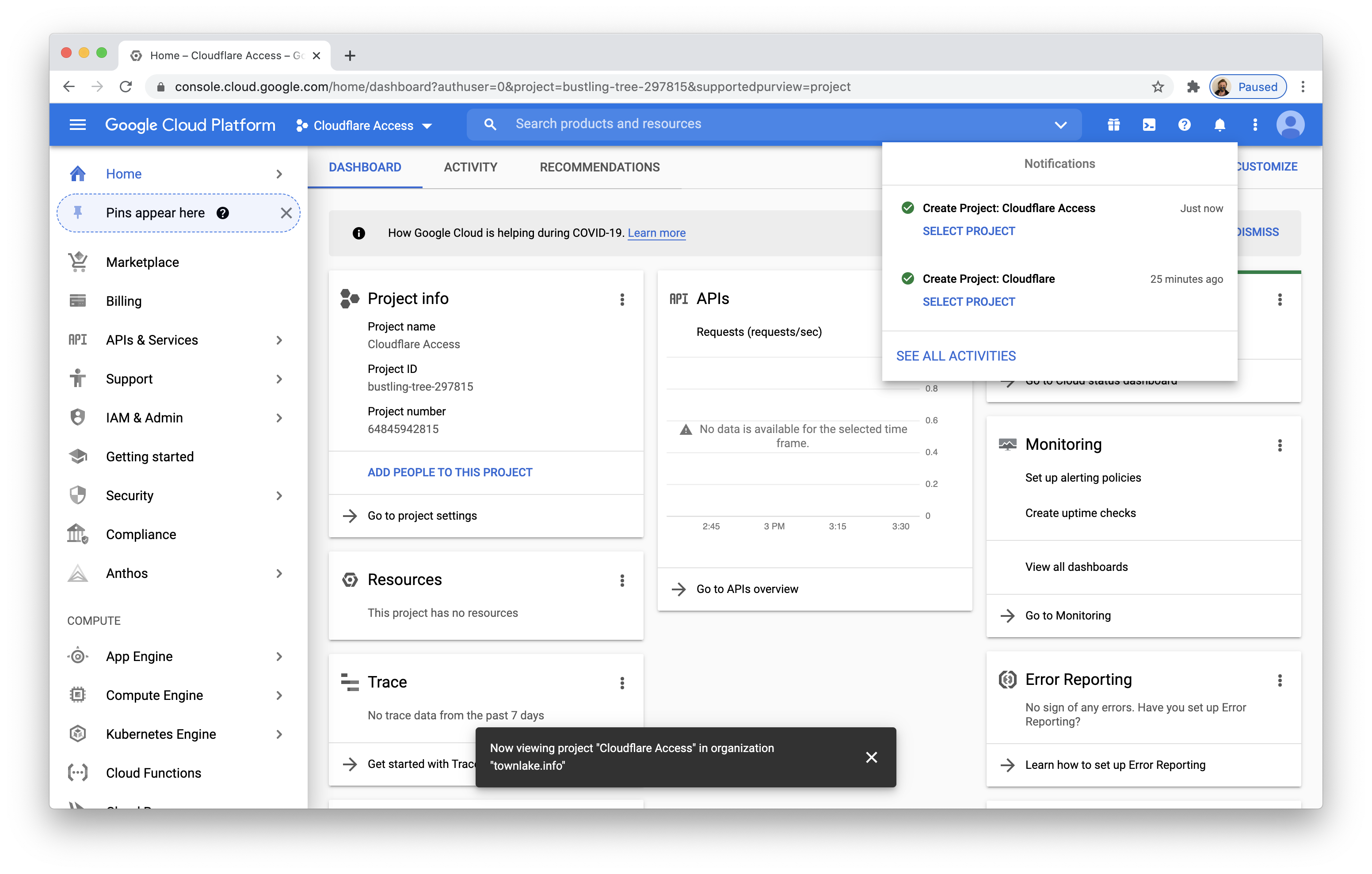
Click Create Project to create a new project. Name the project and click Create. You should now see a Dashboard for your project.
-
On the left-hand side, select
APIs & Servicesand click Dashboard. -
In the screen that loads, click + Enable APIs and Services in the top toolbar.
-
The API Library will load. Search for
adminin the search bar.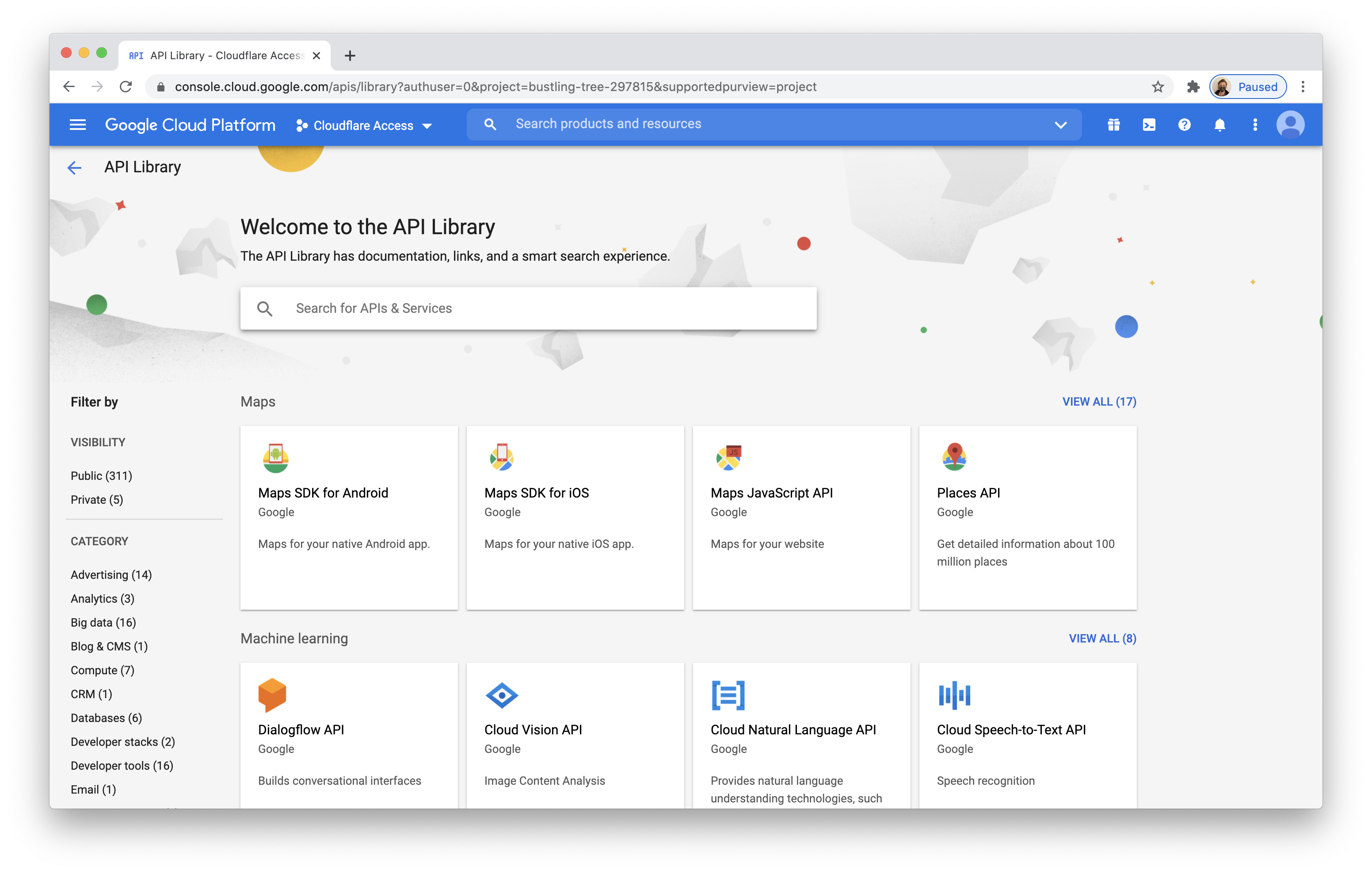
-
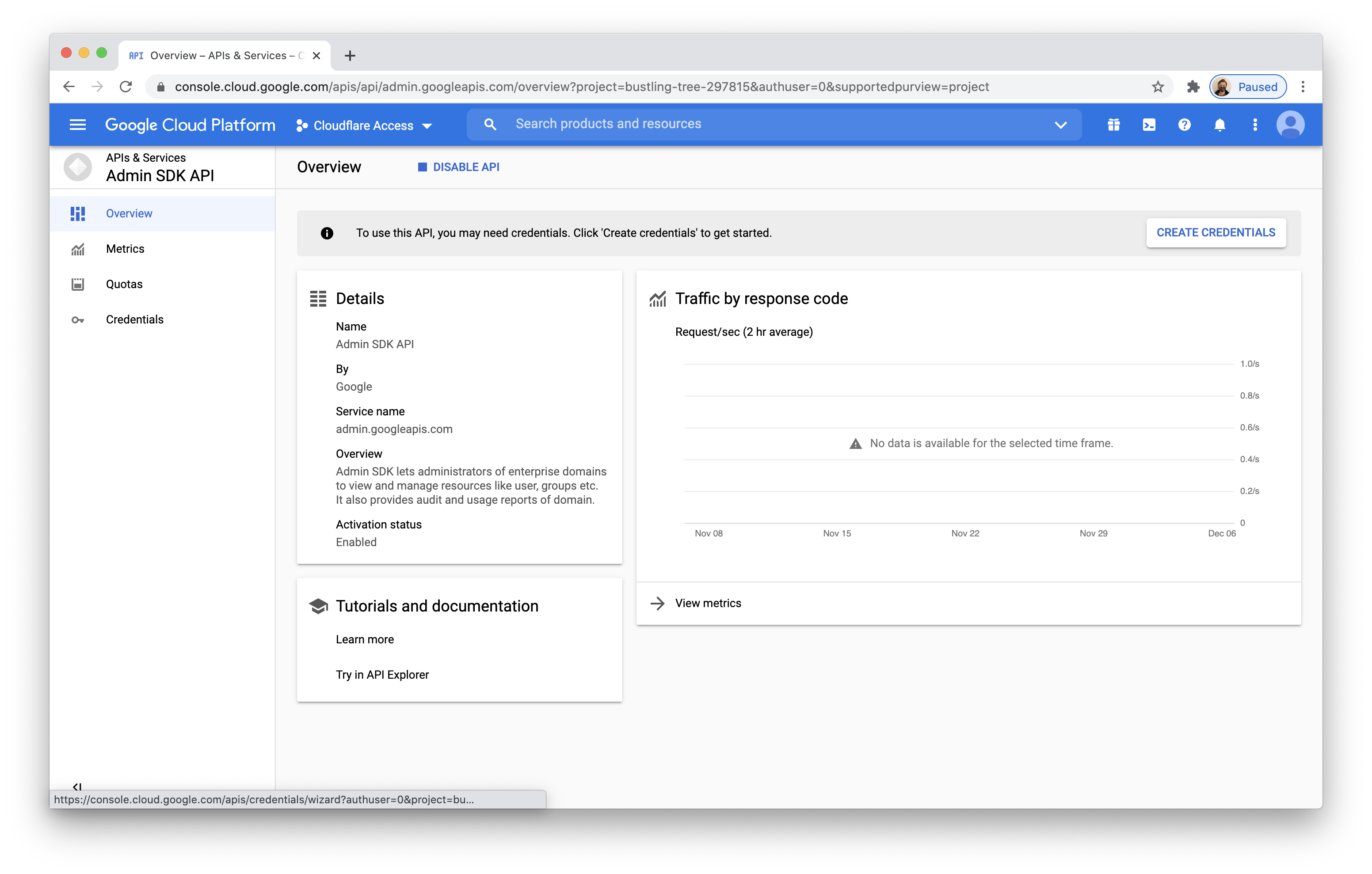
Select
Admin SDK APIby Google. -
Click Enable on the Admin SDK API page. The Admin SDK will be added to your project.
-
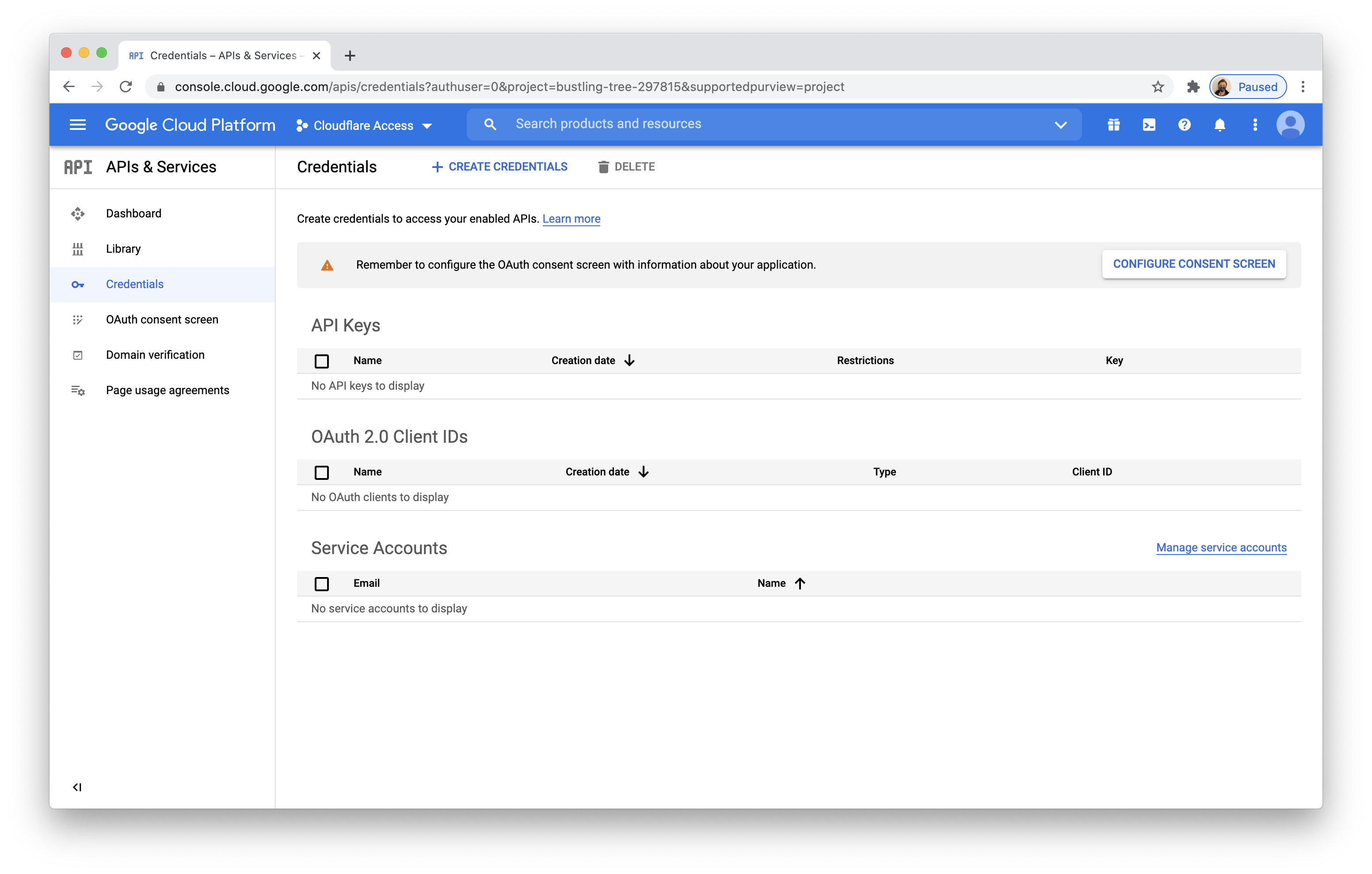
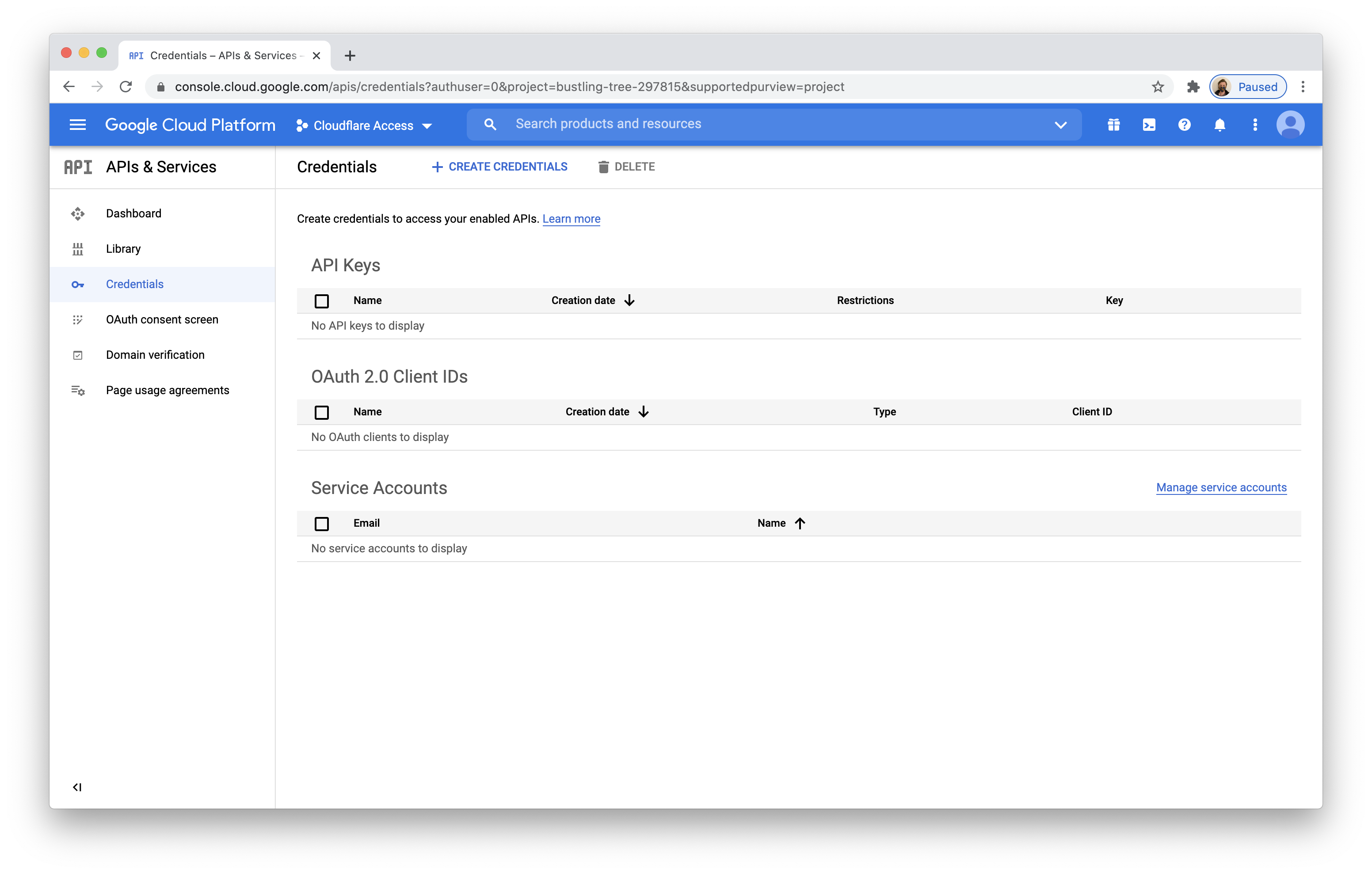
Return to the APIs & Services page. Click Credentials in the navigation bar. You will see a warning that you need to configure a consent screen. Click Configure Consent Screen.
-
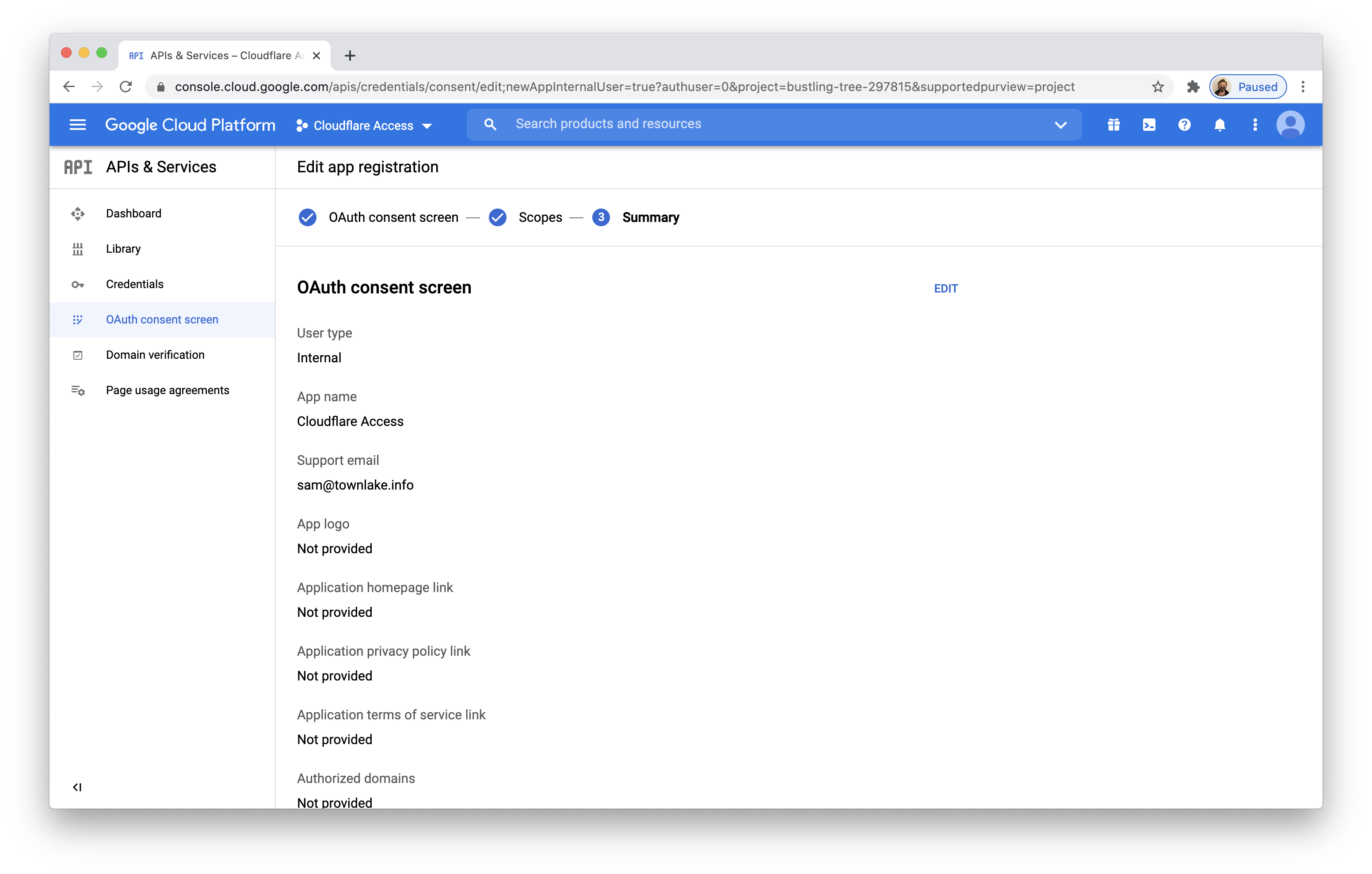
Cloudflare Access will gather information about users in your Google Workspace account, but not other accounts. Toggle
Internalto limit this to members in your account.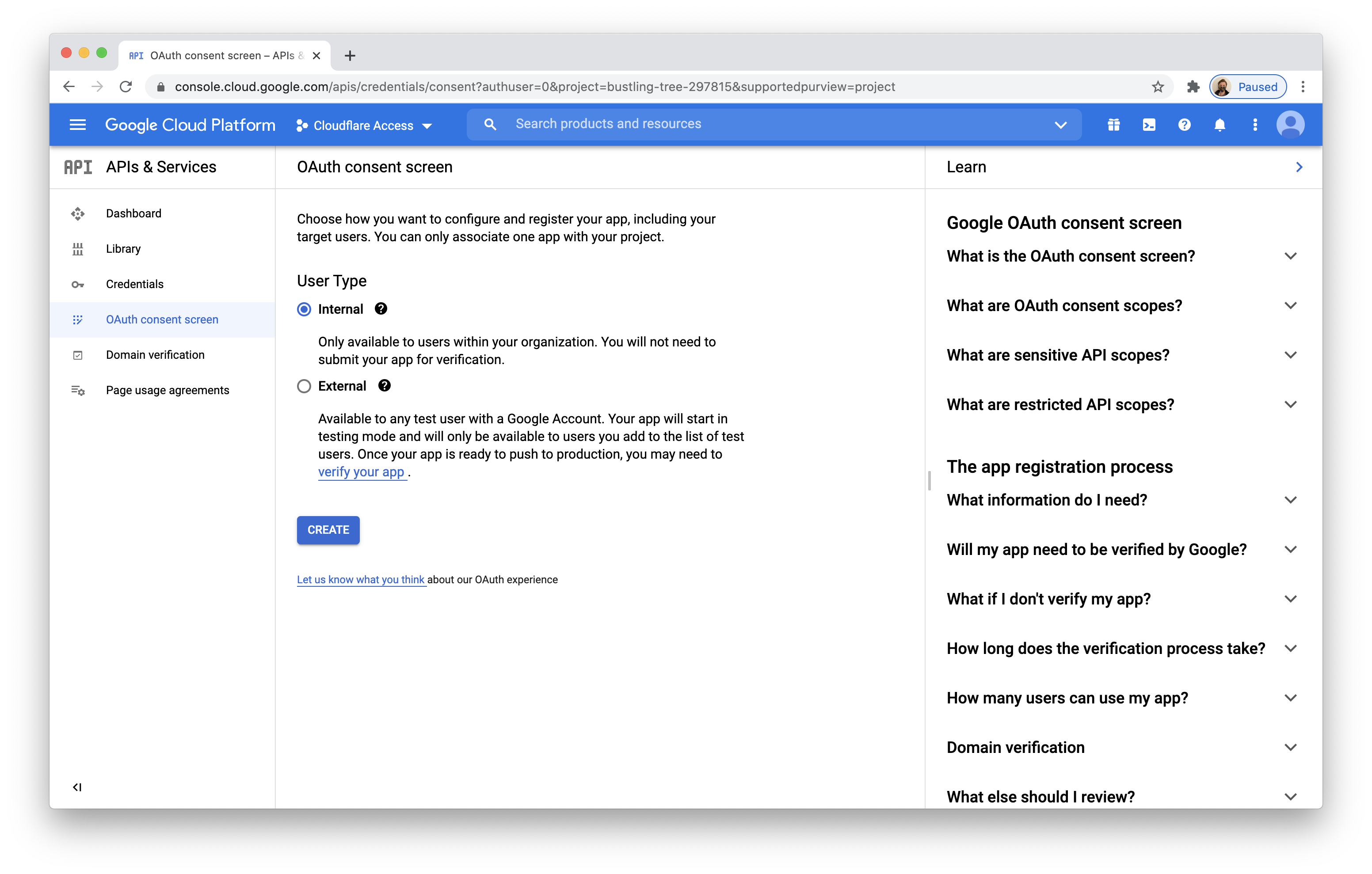
-
Input information about the application.
In this case, you are making an application available to your users and can add your team’s contact information.
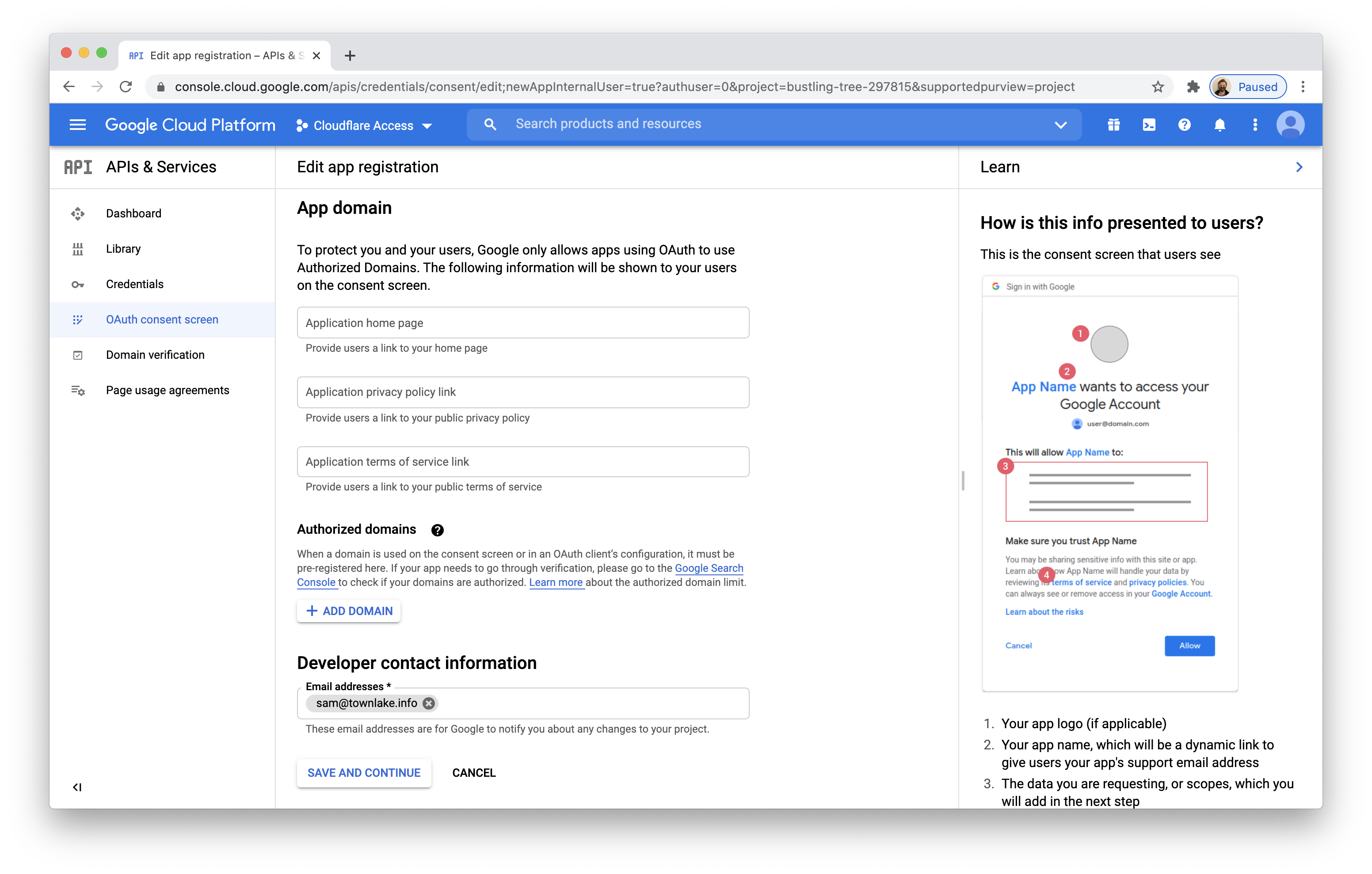
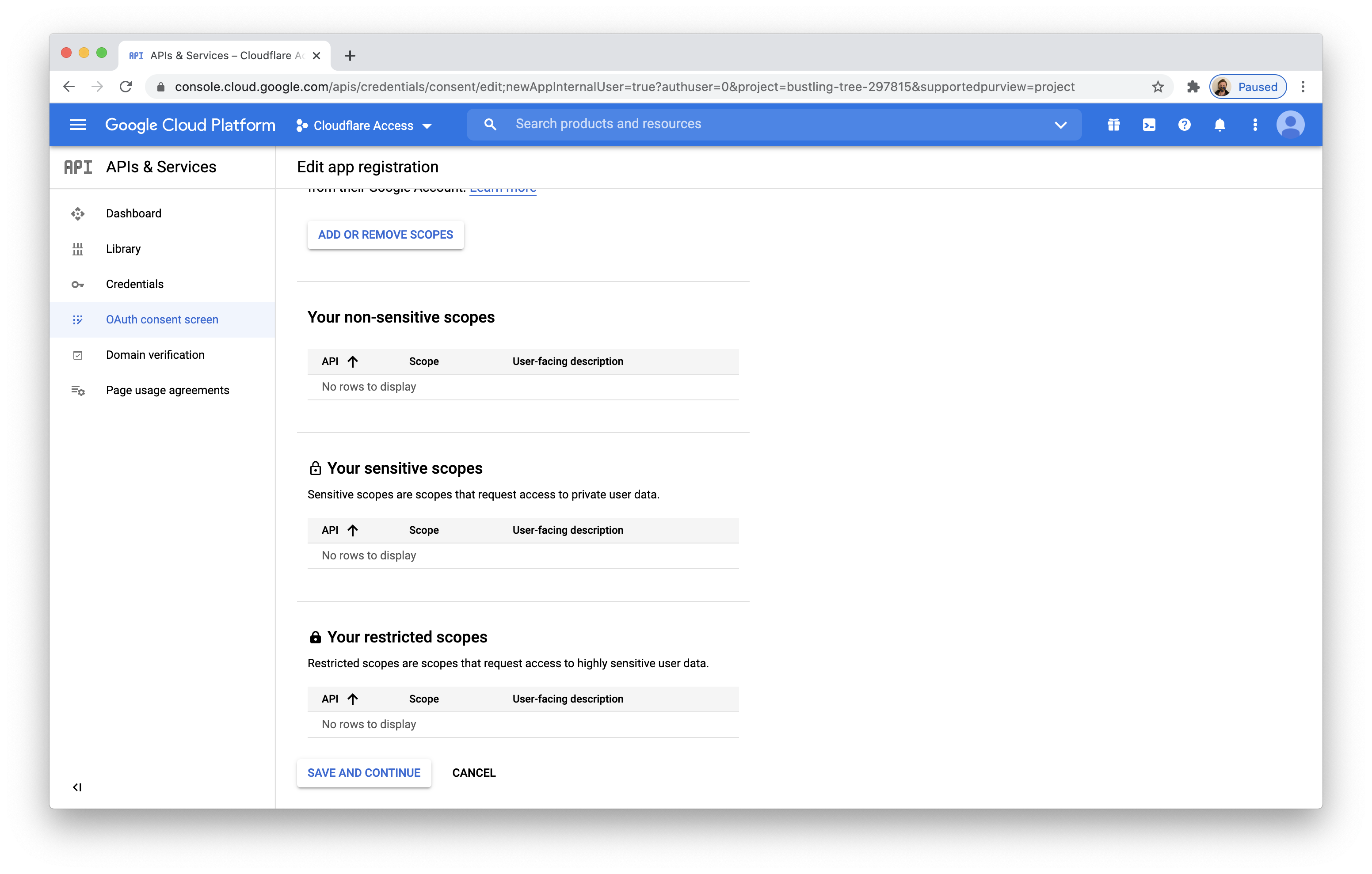
You will not need to configure scopes in this screen and can leave these fields blank.
The summary page will load and you can save and exit.
-
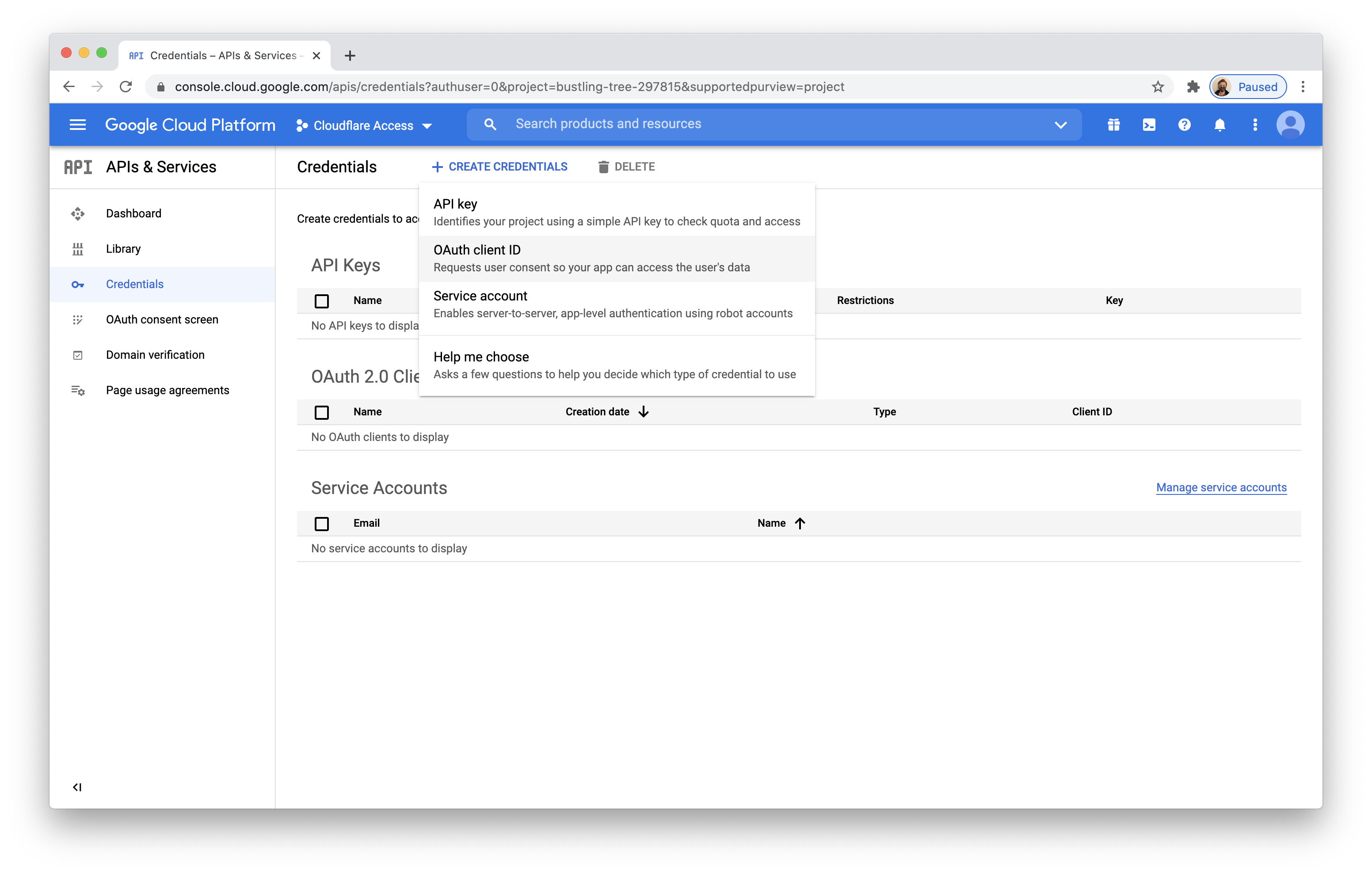
Return to the Credentials page. Click + Create Credentials
-
Select OAuth client ID.
-
Select
Web applicationas the Application type. -
Under Authorized JavaScript origins, in the URIs field, enter your team domain .
-
Under Authorized redirect URIs, in the URIs field, enter your team domain followed by this callback at the end of the path:
/cdn-cgi/access/callback. For example:
https://<your-team-name>.cloudflareaccess.com/cdn-cgi/access/callback
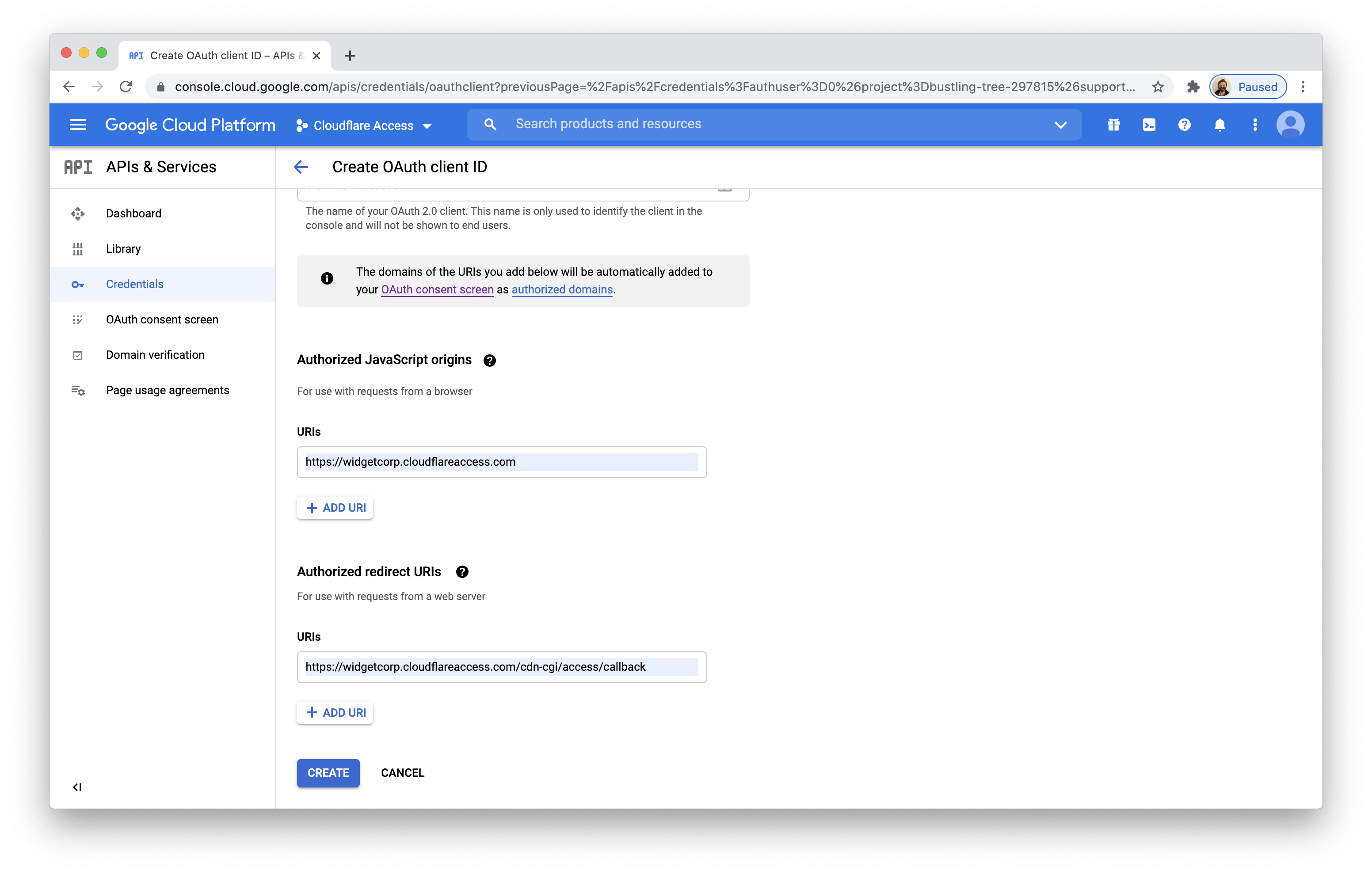
Click **Create**.
-
Google will present the OAuth Client ID and Secret values. The secret field functions like a password and should be kept securely and not shared. For the purposes of this tutorial, the secret field is kept visible. Copy both values.
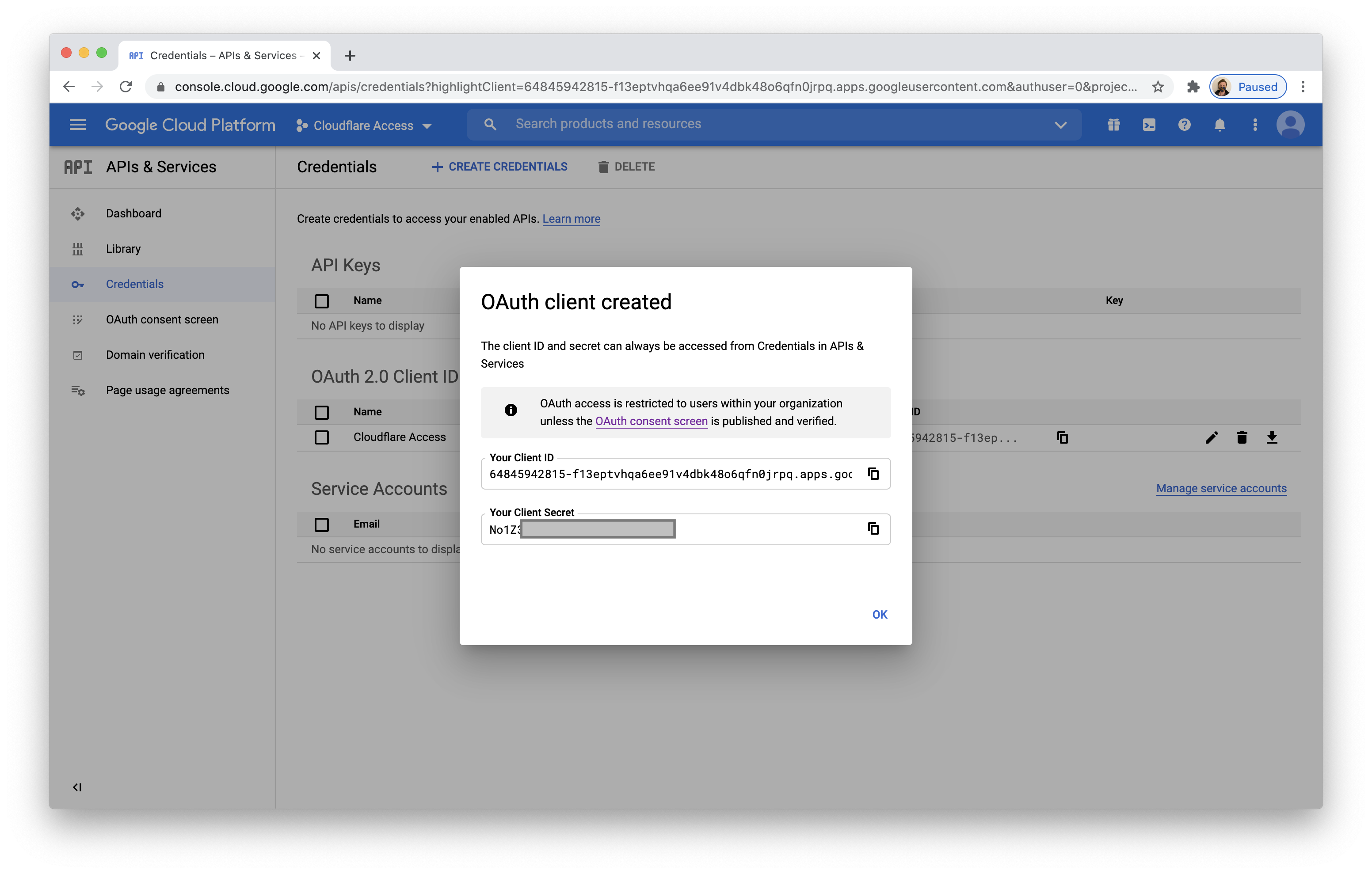
The Client ID will now appear in the
APIs & Servicespage.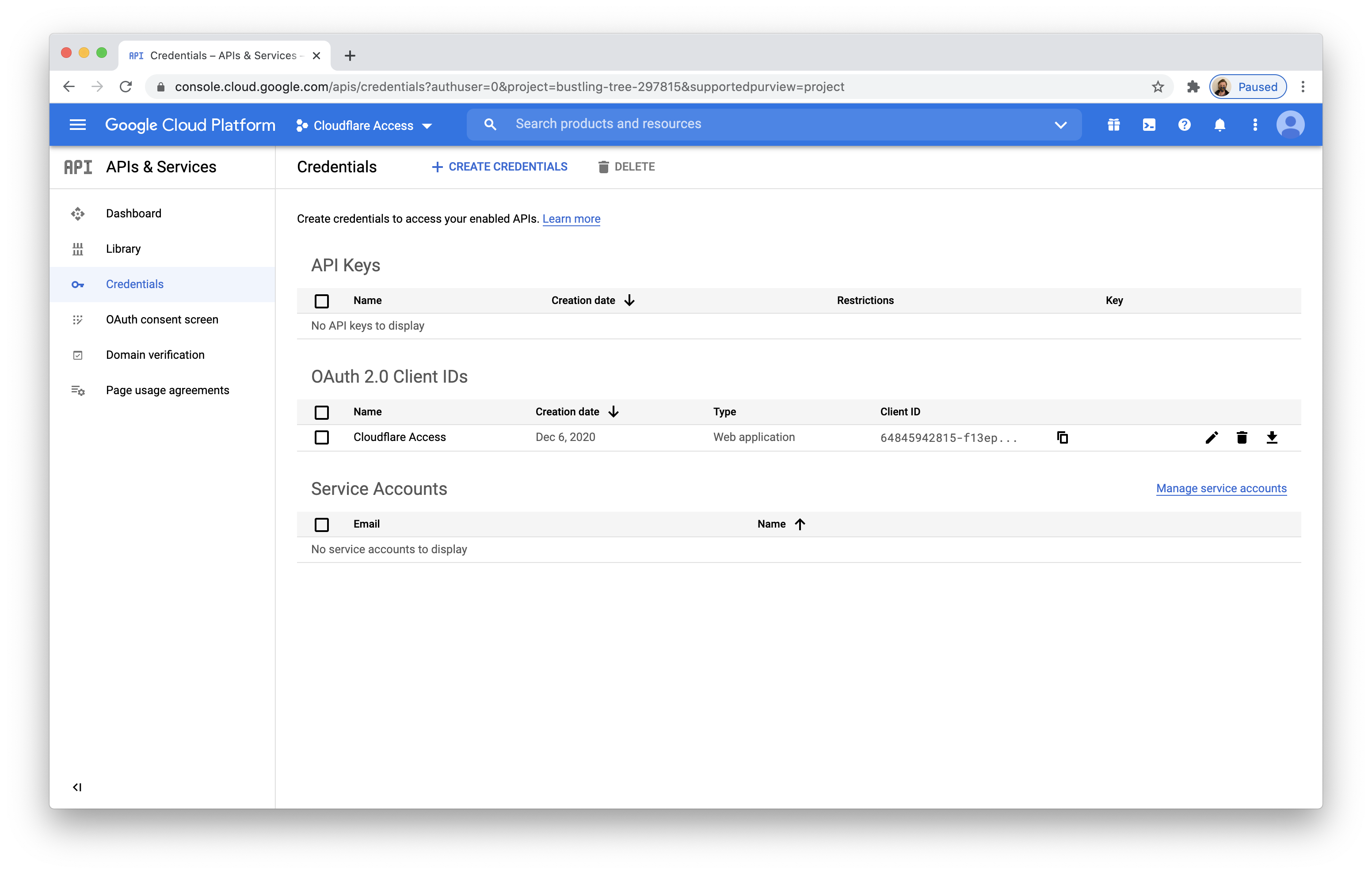
-
On the Zero Trust dashboard, navigate to Settings > Authentication.
-
Under Login methods, click Add new.
-
Select Google Workspace.
-
Input the Client ID and Client Secret fields generated previously. Additionally, input the domain of your Google Workspace account. Click Save.
-
To complete setup, you must scroll below and visit the link generated. If you are not the Google Workspace administrator, share the link with the administrator.
-
The generated link will prompt you to login to your Google account and to authorize Cloudflare Access to view group information.
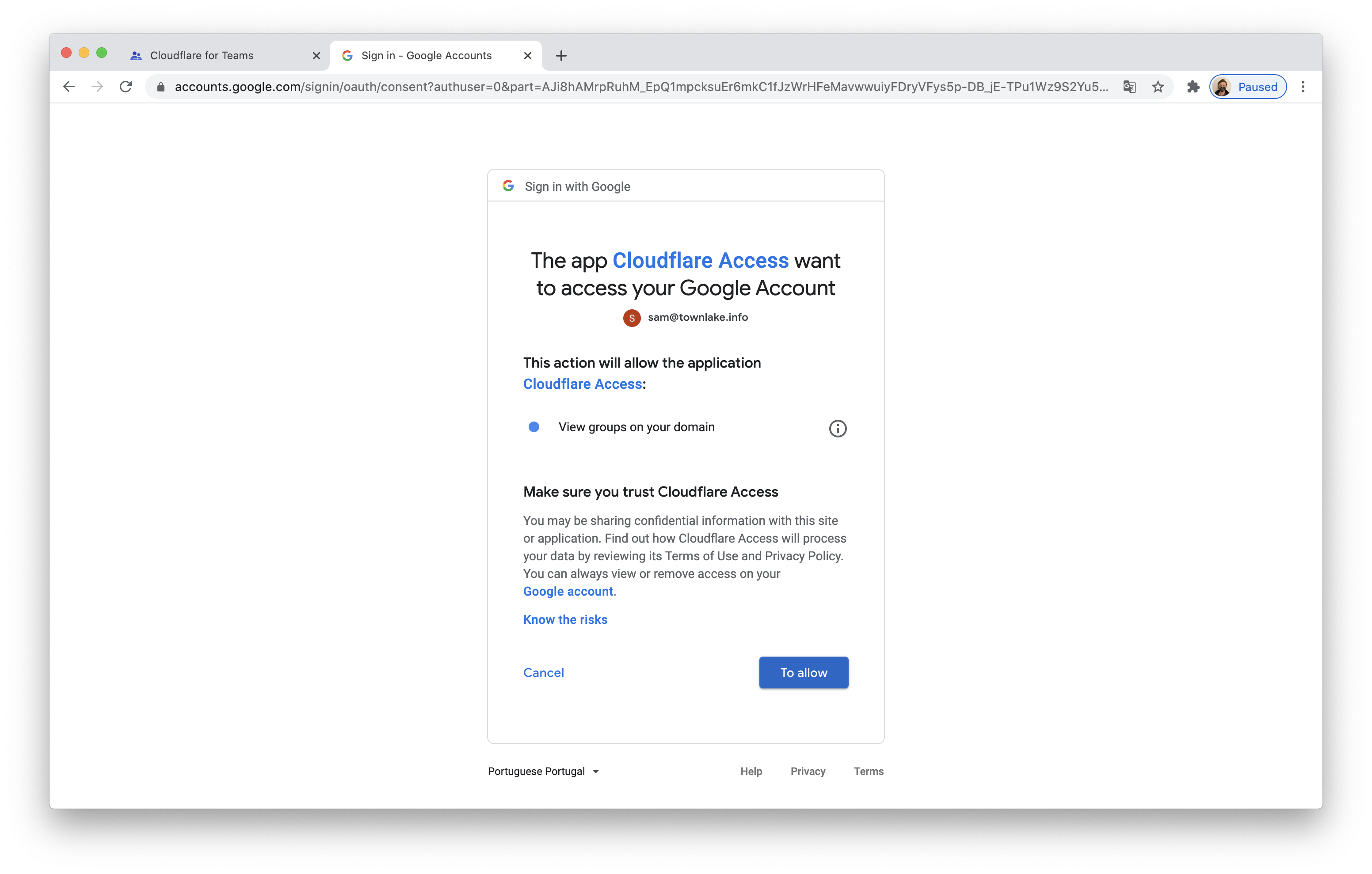
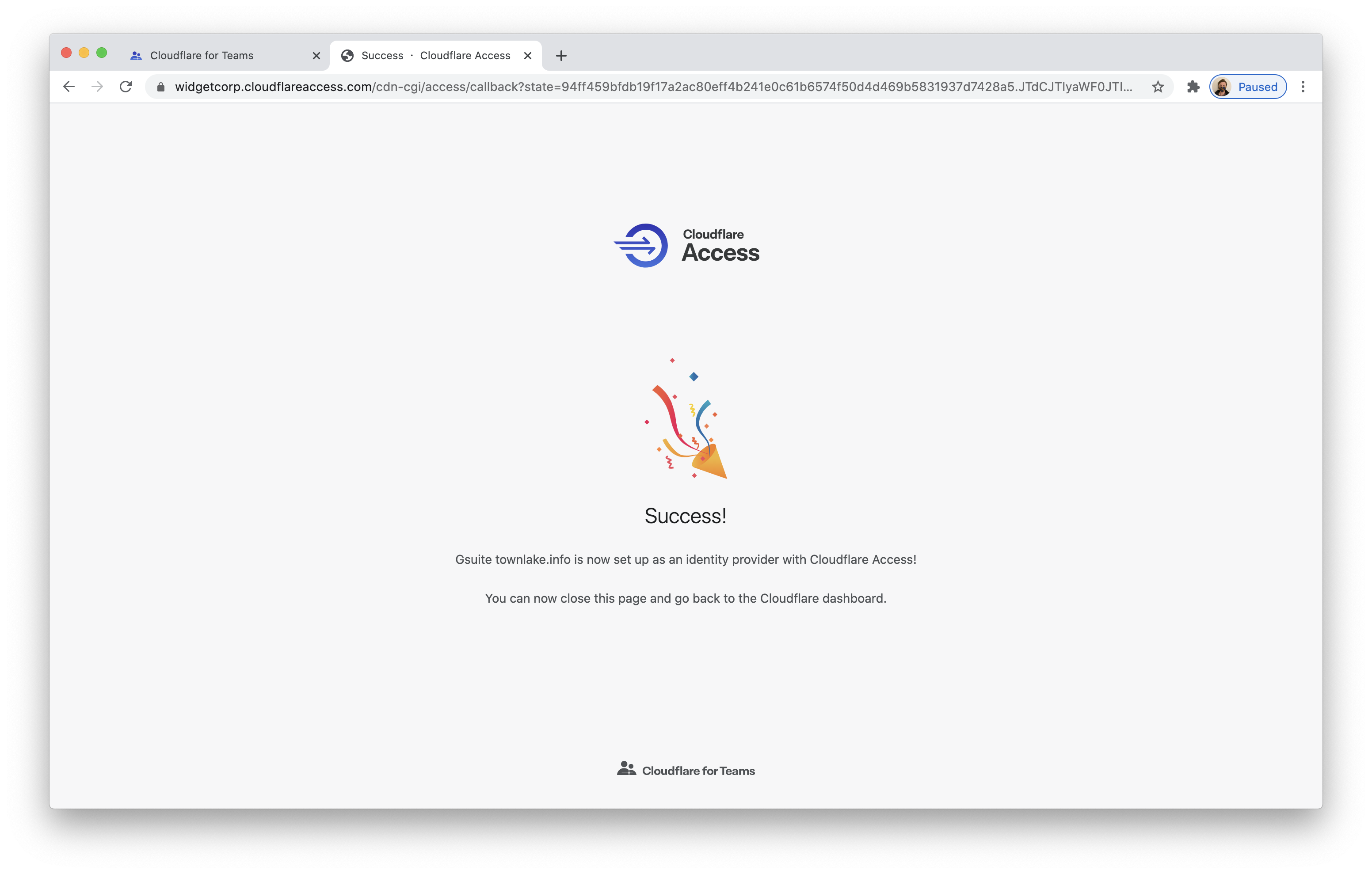
A success page will then load from Cloudflare Access.
-
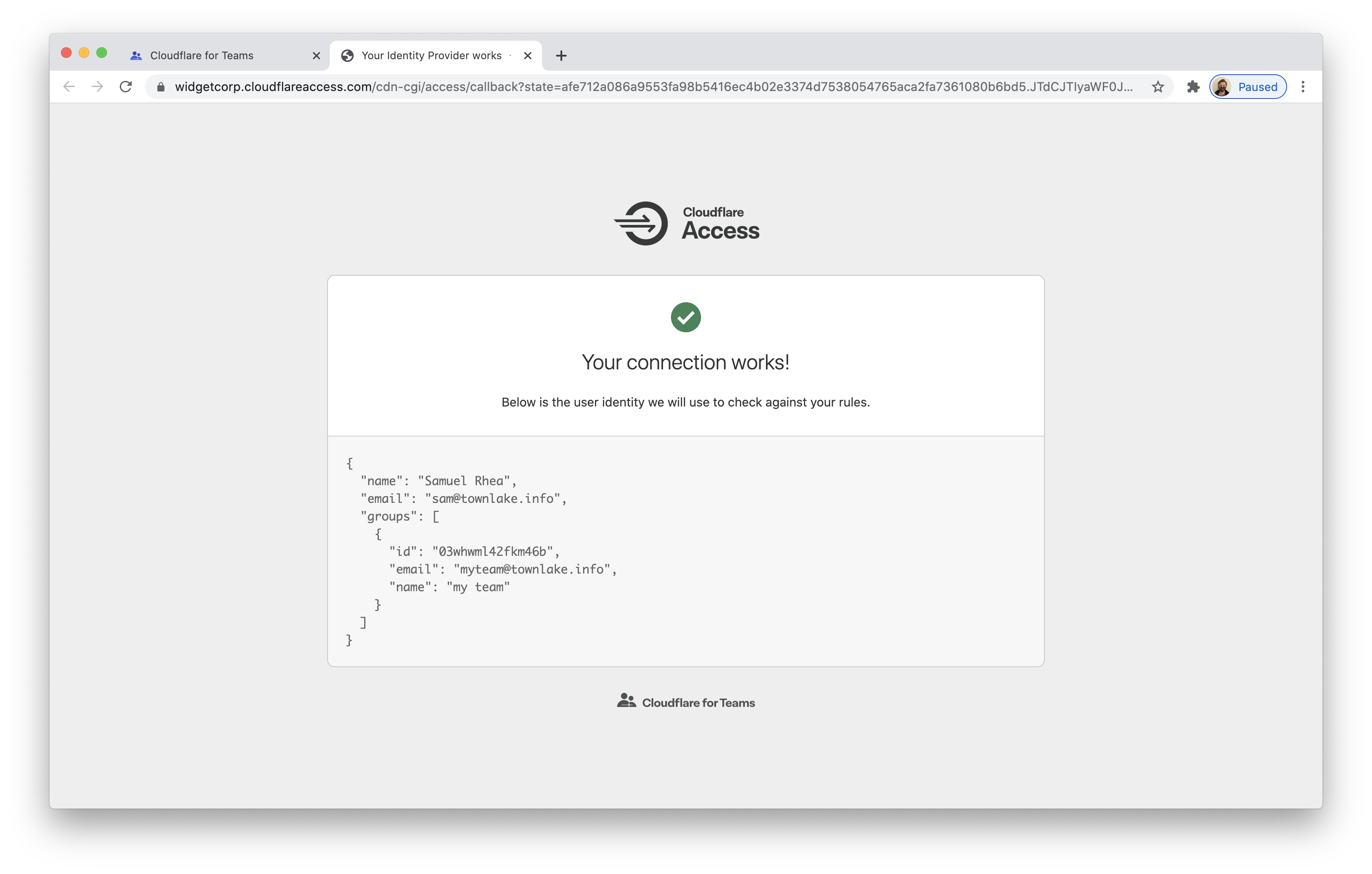
You can now return to the list of identity providers in the Authentication page of the Cloudflare Zero Trust dashboard. Select Google Workspace and click Test.
Your user identity and group membership should return.
Example API Configuration
{
"config": {
"client_id": "<your client id>",
"client_secret": "<your client secret>",
"apps_domain": "mycompany.com"
},
"type": "google-apps",
"name": "my example idp"
}